In 2020, the global average cost of a data breach was $3.86 million (USD). On average it took businesses 207 days to identify the data breach, and 73 days to contain it. Regardless of the size or industry, all businesses are at risk of a data breach as they store valuable information, especially customer data.
For this reason, businesses and security professionals alike are constantly searching for the best method of securing a network from all threats.
Traditionally, most businesses use a castle-and-moat approach to security. This is where the focus of security is on the network perimeter and most of the security investment is in firewalls, proxy servers and preventing intrusion from outsiders. In theory this approach seems logical, however it has some key limitations.
The castle-and-moat approach allows those within the network access to all data. This means that even if the moat is effective at keeping intruders out, it doesn’t stop users with compromised identities or insider threats. It’s also outdated as it was built for traditional networks and does not consider how networks have changed as businesses move to the cloud.
Cyber security and hybrid work
With the workplace fundamentally changing, as hybrid work becomes the new norm, the traditional castle-and-moat approach is no longer viable. When all employees worked in an office space if a machine tried to access a network from outside the office it would raise a red flag. Now with employees working from home it is important to be able to accurately authorise and authenticate users, regardless of where they are physically located.
In order to overcome these limitations businesses must change the way they view network security; this is where the zero trust security model comes in.
What is the zero trust security model?
The zero trust security model assumes that there are malicious actors both inside and outside a network. Therefore, no users or machines are automatically trusted, and all requests must be authenticated and authorised. This verification is based on all data points, including user identity, device health, service or workload, classification and anomalies. Another key principle of the zero trust security model is least-privilege access. This states that users should only have access to the data they need to do their job, and nothing more.
Why move to a zero trust security model?
The zero trust model greatly increases security and is a security model that considers how digital transformations have fundamentally changed businesses and their networks. This is particularly important as many organisations keep their data in the cloud, rather than on-premise.
The modern network does not have clearly defined perimeters to protect, so the zero trust model moves the perimeter to each individual file. This model, especially the least-privilege access principle, significantly reduces the risk of an insider threat. As users can only access the data necessary to do their jobs it means they cannot access sensitive data that could be shared maliciously or accidentally.
How to implement a zero trust security model in your business
There are multiple principles in the zero trust security model, and your business may already have implemented some of the necessary technology. However, transitioning to a comprehensive zero trust security model takes time and significant planning as it involves completely rethinking how a business views security.
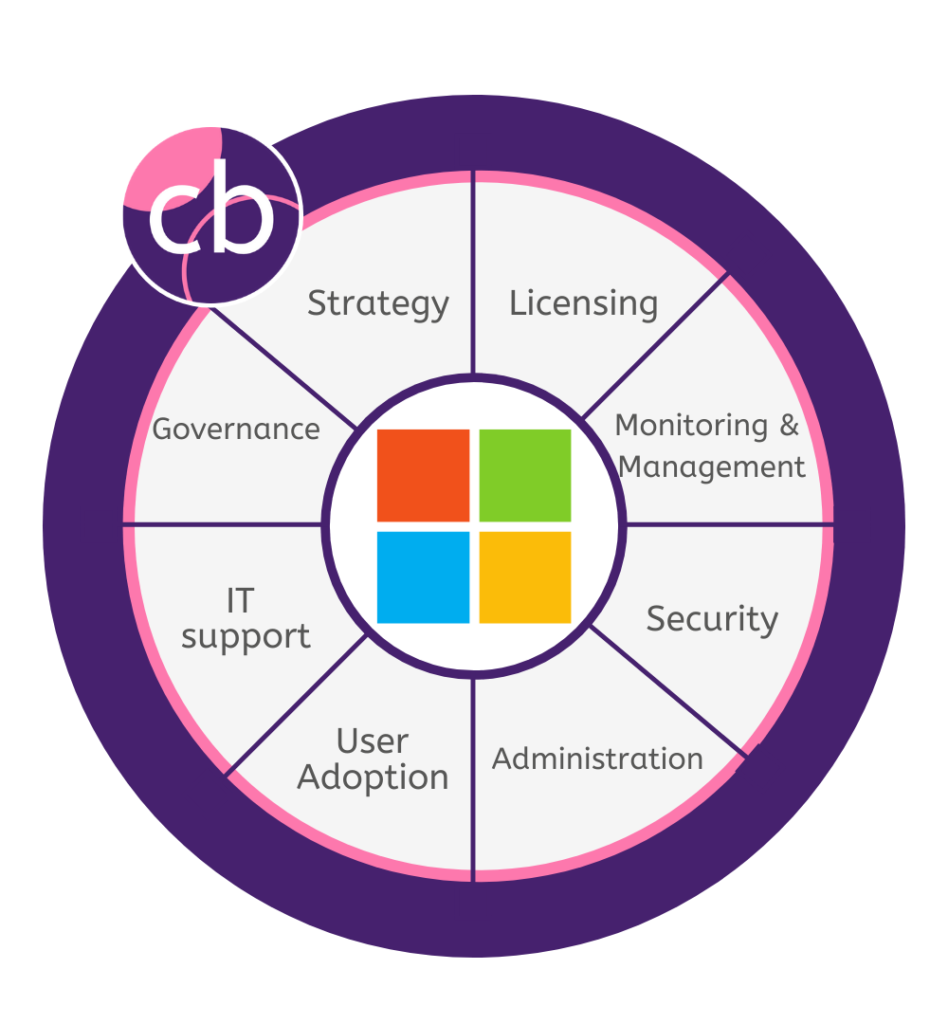
The key to successfully implementing zero trust architecture is to first take inventory of existing mechanisms and technology. It is important to consider how traffic flows through the network and what is currently controlling the flow. From there the business must implement the necessary technologies and policies in line with the zero trust principles. This includes identity access management, endpoint management, in-app permissions, data protection, and infrastructure and network security. Once your business has implemented all the necessary technology and policies it should be regularly reviewed and iterated upon to dynamically enforce policy changes.
The zero trust security model is a modern rethinking of what constitutes a comprehensive security solution for a business. It overcomes the limitations of the castle-and-moat approach and greatly reduces the risk of a data breach, even one due to an insider attack. However, the road to zero trust is not simple, and it takes time and expertise to ensure that all the potential benefits are realised. If your business is considering moving to a zero trust security model, and need some expert advice, please get in touch with our cyber security practice.